NEW CASTLE, N.H.: Several high-level Air Force, joint service and industry speakers discussed the powers and perils of operating in a net-centric environment at this year’s Net-Centric Operations Conference at the Wentworth Hotel and Conference Center here Sept. 20.
Sponsored by the Patriots Roost Chapter of the Association of Old Crows, the conference brought government and industry members together to examine the net-centric landscape and help chart the way forward.
Several speakers discussed cyber threats and applications, while others talked primarily about intelligence, surveillance and reconnaissance requirements. Electronic warfare, including jamming technology and advanced computing power were also discussed.
All of this reinforced a point made by Lt. Gen. William Lord, Air Force chief information officer and chief of warfighting integration.
“Net-centric warfare is not about network warfare,” General Lord said. “Some people think they’re the same thing, but there’s a big difference.”
Failure to recognize that difference creates the potential to “focus on the wrong things,” he said. One example would be offensive cyber operations, which are limited, according to the general.
Net-centric warfare is really about enabling networked operators to tap into all the information they need to “create combat effects that change an enemy’s behavior,” he said.
Cyber, on the other hand, is mostly about defense and about protecting the information network that allows operators to do what they need to do, the general said.
“The network is now so integral to combat operations that you can’t live without it,” he said. “Twenty years ago, when the network went down, who cared?”
Now, however, it has to be completely reliable.
Ron Mason, Air Force program executive officer for cyber and net-centric systems, opened the conference by reminding participants that ‘mission assurance’ is critical.
That means “the integrity and pedigree of our data must be assured,” he said.
He also emphasized, however, that net-enabled operations are not only about cyber, but about integrating “terrestrial, air, space and cyber networks.”
Within the ISR community, that integration is essential, according to Maj. Gen. James Poss, Air Force assistant deputy chief of staff for ISR. He stressed that capabilities and effects, not platforms, matter most.
“ISR is the mother of all domain-neutral missions,” he said. “We are target-focused and domain-agnostic. We couldn’t care less whether we get that ISR data from a human engine, from a spacecraft, through cyber means or from an aircraft, as long as we get it.”
General Poss spoke about ISR’s evolution, saying early data sharing efforts were useful but hardly net-centric.
“Then about 2001, with the tremendous help of a bunch of folks from the Electronic Systems Center (at Hanscom Air Force Base, Mass.), we broke the code on the beginnings of true net-centricity,” he said. “That’s when we figured out how to take our big sites and swap information back and forth between them.”
However, while the ones and zeros flowed freely, command and control — the ability to tie the information together and use it for effective, timely decision-making — still lagged. It took a few more years to get to that point.
“Now we’re about to see yet another explosion when we’re really able to get all this fantastic data to the tactical edge,” General Poss said, again cautioning that it might take time to get the command and control piece right.
General Poss also focused on the advantages of distributed and split operations. Borrowing a phrase from the environmental movement, he said net-enabled intelligence operations allow the Air Force to think globally but act locally.
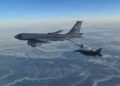
“We can literally, using the miracle of satellite and beyond-the-line-of-sight communications, fly (an MQ-1) Predator over Afghanistan or Iraq out of Las Vegas,” he said.
These sorts of operations provide the ideal mission for the Air National Guard, he said, noting that benefits go well beyond allowing them to ‘work from home.’
Keeping Airmen out of harm’s way is certainly one benefit. Air Force officials estimate that it keeps about 6,500 Airmen out of theater, including all the additional required support personnel, through such operations.
Reducing these deployment requirements saves money, as well, while increasing effectiveness. One major way: allowing Guard forces to conduct missions with a continuity that rotational forces simply could not maintain, General Poss said.
“Using the power of distributed operations, you can assign specific nodes with specific primary and secondary targets that are specific parts of real estate in Southwest Asia,” he said.
In some cases, the same Air National Guard operator has been looking at the same locations for five or six years.
Yet for all this power, the reliance on net-enabled capabilities brings dangers, too.
Dr. Davy Belk, director of the Air Force Research Laboratory’s Information Directorate, acknowledged this at the outset of his briefing.
“Naïve implementation of net-centric ops will be exploited by our adversaries,” he said. “So how do we keep the benefits and get rid of the negatives?”
Doctor Belk then proposed a number of steps, including sensibly scaling cyber defense to meet the need — 100 percent assurance for nuclear matters, for instance — but something less for routine desktop computing. He also suggested a cyber strategy that calls for avoiding most attacks and surviving others, then recovering quickly and defeating the threat.
Industry expert Hayri Tarhan of Oracle added that “hiding behind a firewall is no longer sufficient.”
He said encryption and other more sophisticated measures, used in concert, are needed to meet current and evolving threats.
Air Force acquisition efforts need to be increasingly agile to respond to those threats, said Rich Lombardi, ESC executive director. Among a number of issues and initiatives, he discussed the Cyber Safari program office now being stood up at ESC.
“Our intent is to provide a lean, multi-functional team that will be armed with streamlined processes and procedures and be able to get rapid capabilities out to the warfighter,” he said.